Free and Open decentralized data store
Tahoe-LAFS (Tahoe Least-Authority File Store) is the first free software / open-source storage technology that distributes your data across multiple servers. Even if some servers fail or are taken over by an attacker, the entire file store continues to function correctly, preserving your privacy and security.
Table of contents
💡 About Tahoe-LAFS
Tahoe-LAFS helps you to store files while granting confidentiality, integrity, and availability of your data.
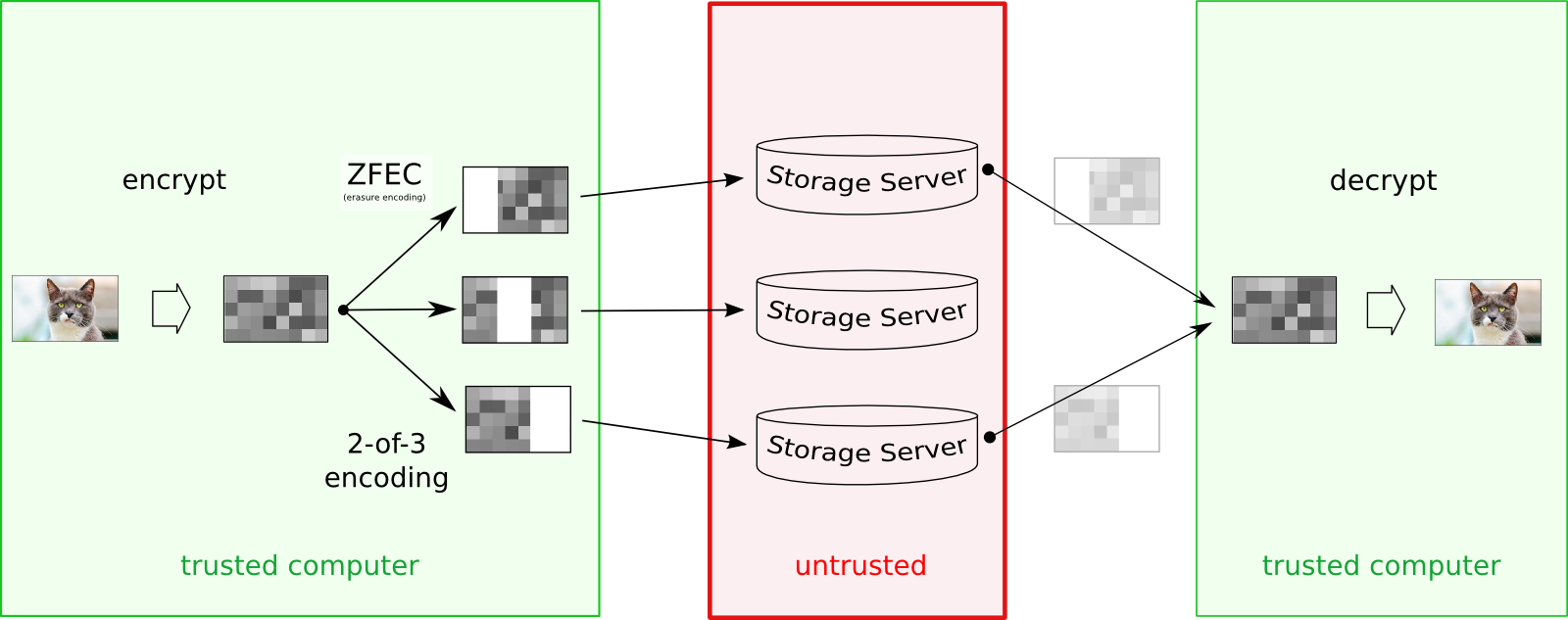
How does it work? You run a client program on your computer, which talks to one or more storage servers on other computers. When you tell your client to store a file, it will encrypt that file, encode it into multiple pieces, then spread those pieces out among various servers. The pieces are all encrypted and protected against modifications. Later, when you ask your client to retrieve the file, it will find the necessary pieces, make sure they haven’t been corrupted, reassemble them, and decrypt the result.
The client creates pieces (“shares”) that have a configurable amount of redundancy, so even if some servers fail, you can still get your data back. Corrupt shares are detected and ignored so that the system can tolerate server-side hard-drive errors. All files are encrypted (with a unique key) before uploading, so even a malicious server operator cannot read your data. The only thing you ask of the servers is that they can (usually) provide the shares when you ask for them: you aren’t relying upon them for confidentiality, integrity, or absolute availability.
Tahoe-LAFS was first designed in 2007, following the "principle of least authority", a security best practice requiring system components to only have the privilege necessary to complete their intended function and not more.
Please read more about Tahoe-LAFS architecture here.
✅ Installation
For more detailed instructions, read docs/INSTALL.rst .
Once tahoe --version works, see docs/running.rst to learn how to set up your first Tahoe-LAFS node.
🤖 Issues
Tahoe-LAFS uses the Trac instance to track issues. Please email jean-paul plus tahoe-lafs at leastauthority dot com for an account.
📑 Documentation
You can find the full Tahoe-LAFS documentation at our documentation site.
💬 Community
Get involved with the Tahoe-LAFS community:
- Chat with Tahoe-LAFS developers at #tahoe-lafs chat on irc.freenode.net or Slack.
- Join our weekly conference calls with core developers and interested community members.
- Subscribe to the tahoe-dev mailing list, the community forum for discussion of Tahoe-LAFS design, implementation, and usage.
🤗 Contributing
As a community-driven open source project, Tahoe-LAFS welcomes contributions of any form:
Before authoring or reviewing a patch, please familiarize yourself with the Coding Standard and the Contributor Code of Conduct.
❓ FAQ
Need more information? Please check our FAQ page.
📄 License
Copyright 2006-2020 The Tahoe-LAFS Software Foundation
You may use this package under the GNU General Public License, version 2 or, at your option, any later version. You may use this package under the Transitive Grace Period Public Licence, version 1.0, or at your choice, any later version. (You may choose to use this package under the terms of either license, at your option.) See the file COPYING.GPL for the terms of the GNU General Public License, version 2. See the file COPYING.TGPPL for the terms of the Transitive Grace Period Public Licence, version 1.0.
See TGPPL.PDF for why the TGPPL exists, graphically illustrated on three slides.